I'm testing Azure Graph API.
and I'm trying to find an API that allows me to retrieve only users that are assigned to a specific app I created.
In app registration page, I gave a user.read.all permission, but the get user API gives me all users that are in the AD and not only that are assigned to the app I created. Should I change the permissions? or to access an another API?
Does anybody know what to do?
Thanks
CodePudding user response:
As a workaround you can use the below graph API to get the list of users.
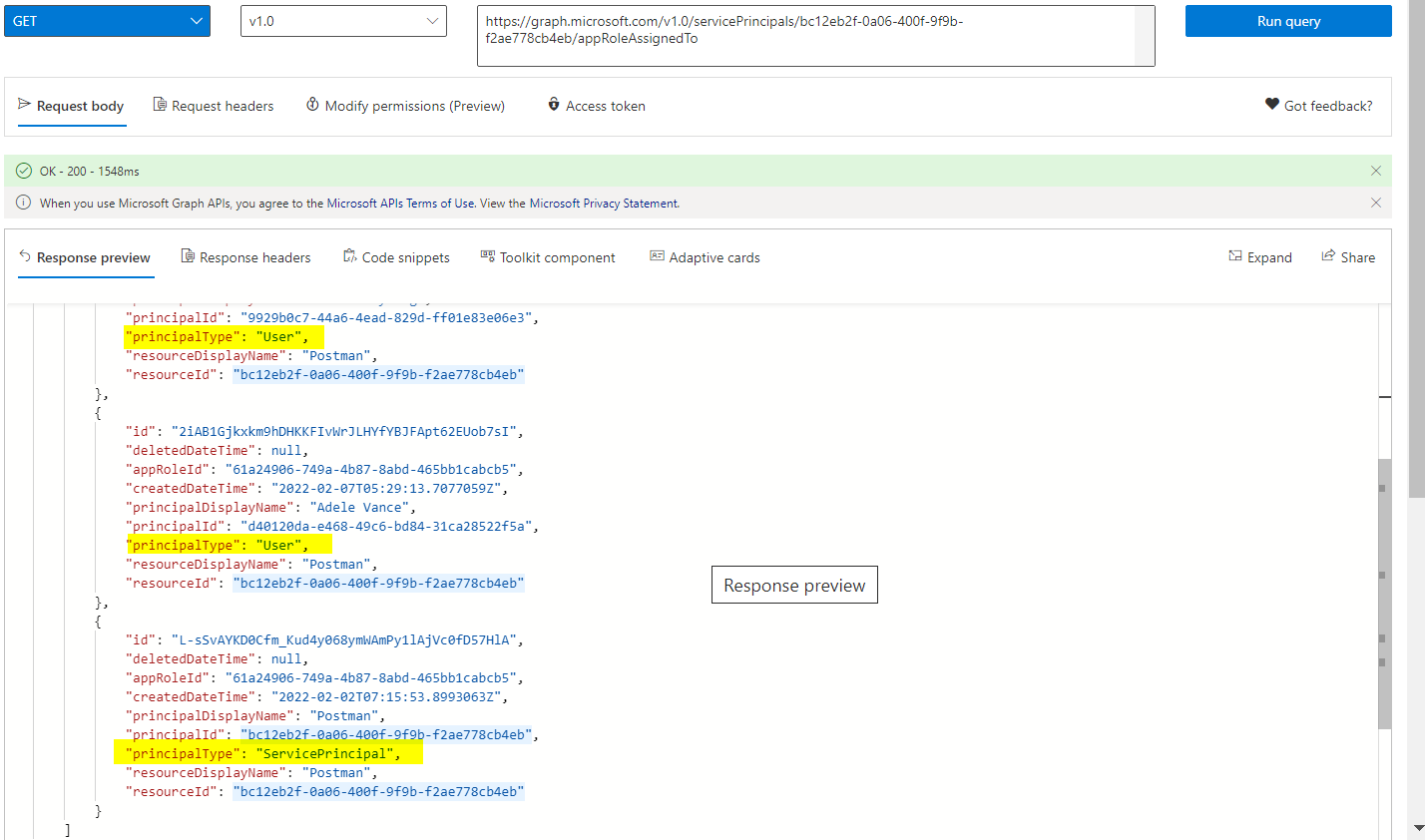
https://graph.microsoft.com/v1.0/servicePrincipals/{ObjectID}/appRoleAssignedTo
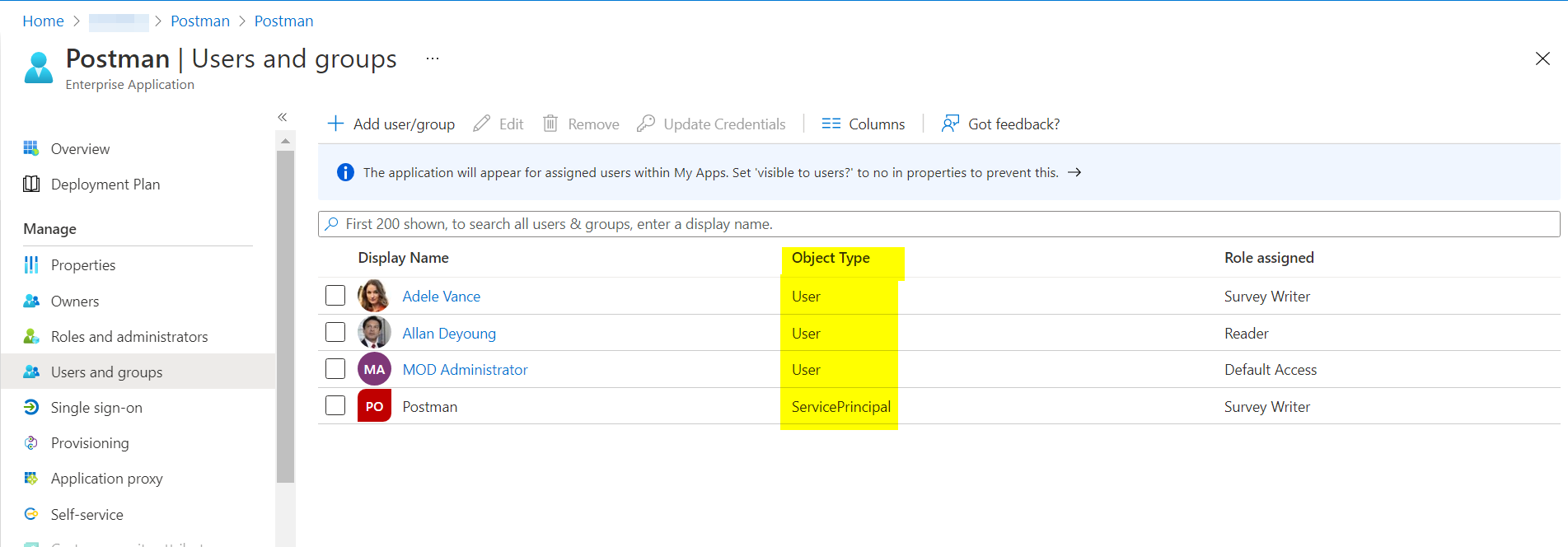
Note: The above graph API gives the Object Types User and Service Principle as well
As discussed in the MS Q &A Platform This endpoint currently does not support filters based on appRoleId. In fact, except that the id parameter can be filtered, the three parameters appRoleId, principalId, and resourceId do not support filtering. Similar issues have been raised before.
CodePudding user response:
Additionally, This object id should be based on service principal and not the application registration here. You can retrieve the object Id from Azure AD->Enterprise Applications->Your app->object ID.
You need to have at least Application.Read.All and Directory.AccessAsUser.All for delegated permissions or Application.Read.All for application permission based on user or application context.
For specific details, you can add $select parameter to show only the displayName of the users assigned to the app.
https://graph.microsoft.com/v1.0/servicePrincipals/{object Id}/appRoleAssignedTo?$select=principalDisplayName