I'm currently experimenting AES encryption using Google App Script, and I found out about cCryptoGS.
It feels weird, as like all ciphered texts seem to start with U2FsdGVkX1 (even though I change the part this is my passphrase in the example to something else very very different). I am not sure if I remembered correctly, I once tried AES in the past, but on Nodejs, and it looked just so much different, I'll get completely different text ciphered out even if I change only a single character in either my message, or my key.
CodePudding user response:
CryptoJS can process both passphrases and keys for encryption and decryption. Strings are interpreted as passphrases, WordArrays as keys, s. The Cipher Input.
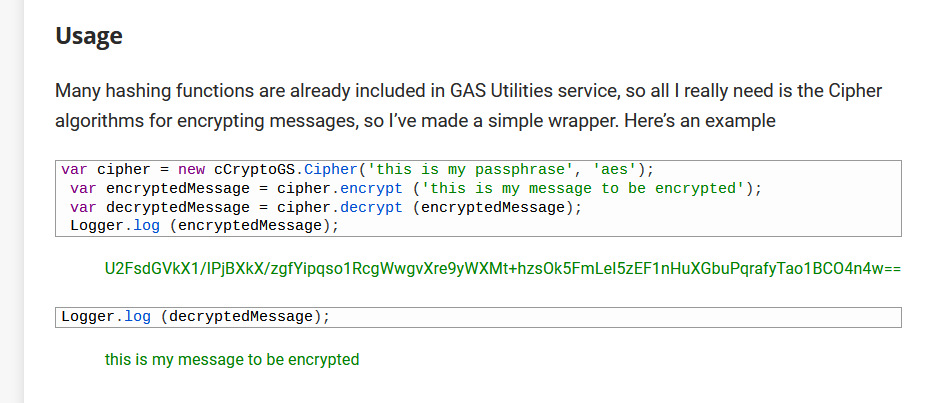
cCryptoGS wraps the passphrase variant and supports the algorithms AES, DES, TripleDES and Rabbit, see Usage.
E.g. for AES, cCryptoGS/CryptoJS encrypts with AES-256, whereby a passphrase must be passed in addition to the plaintext.
Before encryption a random 8 bytes salt is generated and from passphrase and salt a 32 bytes key and 16 bytes IV is derived with the OpenSSL key derivation function EVP_BytesToKey().
The result is generated in OpenSSL format for compatibility with OpenSSL, which consists of the ASCII encoding of Salted__ followed by the 8 bytes salt and the actual ciphertext, with the entire expression Base64 encoded.
The Base64 encoding of Salted__ is U2FsdGVkX18=, where U2FsdGVkX1 is fixed (the last two characters depend on the 1st byte of the salt and can therefore change). Thus, any encryption starts with U2FsdGVkX1, but this does not reveal any information.
So yes, it is encrypted with AES-256, and the constant prefix U2FsdGVkX1 is not critical.
However, the key derivation function EVP_BytesToKey() is deemed insecure nowadays, especially with the parameters used by cCryptoGS/CryptoJS (broken MD5 digest and an iteration count of 1), s. e.g. here, 3rd part, so its use cannot actually be recommended (apart for compatibility maybe).
This applies to the wrapped functionalities that use passphrases for encryption/decryption. cCryptoGS also directly allows the use of CryptoJS functions, see CryptoJS direct, whose security is to be assessed individually.
The secure way is to pass key and IV directly, or when using a passphrase not to apply the built-in function EVP_BytesToKey(), but a reliable key derivation function like PBKDF2.
These variants are supported by CryptoJS, but apparently not by cCryptoGS, at least not by the wrapped functionalities.
Also note that at least the linked cCryptoGS sources seem to be based on CryptoJS version 3.1.2 which is from 2013, s. cCryptoGS sources (current CryptoJS version is 4.1.1).