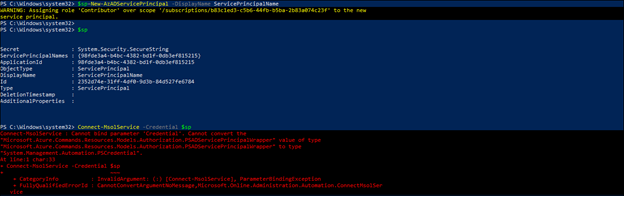
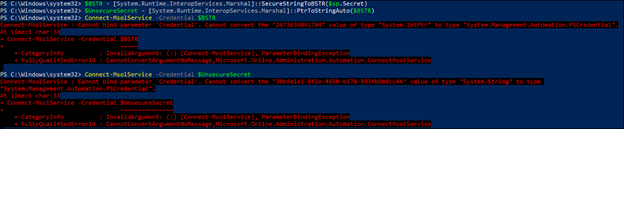
Wrote the below script to get the MFA status for all admins. Works well. But I want to run this using the credential of a service principal and looks like Connect-MsolService does not have an option to do that. Alternatively, Connect-AzAccount has the option to do that but in Az Powershell I dont find a way to get the MFA details of the users.
Is there a way to get the MFA details of the user using service principal?
Connect-MsolService
$output_file_location = "c:\temp\azure_admins_mfa_status_" $(get-date -f yyyy-MM-dd-HH-mm-ss) ".csv"
$admin_roles = "Company Administrator","Billing Administrator","Conditional Access Administrator","Exchange Service administrator","Helpdesk administrator","Password administrator","Security administrator","Sharepoint Service administrator"
# Gets all the members in the admin roles in the roles list above
# Gets the MFA status for each member
# Appends the below data points to a file specified in the $output_file_location variable
# DisplayName,E-mail,Role,MFA-Requirements, MFA-Methods, MFA-MethodsDefault
function get-mfs-status
{
foreach ($roleName in $admin_roles)
{
write-output $roleName
$members = Get-MsolRoleMember -RoleObjectId $(Get-MsolRole -RoleName $roleName).ObjectId
#write-output $members
foreach ($member in $members)
{
write-output $member.EmailAddress
}
foreach ($member in $members)
{
write-output $member
Get-MsolUser -UserPrincipalName $member.EmailAddress | select DisplayName, `
@{N='E-mail';E={$_.userPrincipalName}}, `
@{N='Role';E={$roleName}}, `
@{N='MFA-Requirements';E={(($_).StrongAuthenticationRequirements.state)}}, `
@{N='MFA-Methods';E={(($_).StrongAuthenticationMethods.MethodType)}}, `
@{N='MFA-MethodsDefault';E={($_.StrongAuthenticationMethods | where isdefault -eq 'true').MethodType}} `
| select DisplayName,E-mail,Role, MFA-Requirements, MFA-Methods, MFA-MethodsDefault| Export-Csv $output_file_location -Append `
}
}
}
get-mfs-status
CodePudding user response:
• No, you cannot retrieve the MFA details of the users in an Azure AD using service principal through powershell because service principal is generated for an instance of Azure resource, not an identity which has already been assigned an Azure AD role regarding the scope that has been defined with it. Thus, as an identity though of an Azure AD administrator has the scope of the whole subscription which hosts multiple tenants of your organization, has been defined with some roles and assignments pertaining to that scope. You can create a service principal with that ID logged in to Azure Powershell for the scope of your signed in ID but cannot retrieve the MFA status of users in Azure AD because when you pass the service principal in a variable to pass it as a credential and log in to the Microsoft 365 online, it cannot actuate them to the identity credentials and M365 doesn’t consider it.
Also, to get the status of MFA details of the users, you must connect to MS Online, you cannot retrieve it through Azure AD. Even if you convert the service principal secret in plain text and pass it as a credential to connect to M365, it doesn’t consider it nor it actuates the credentials.
• Instead, if you log into Azure/M365 using your actual credentials, i.e., ID and password, you will be able to retrieve the details provided you have the required role assignments and access.
Reference link for service principal usage: - https://docs.microsoft.com/en-us/powershell/azure/create-azure-service-principal-azureps?view=azps-6.6.0
CodePudding user response:
It's beta but how about that:
