I have a multi-tenant app registered in my Azure tenancy (TENANT A). I am trying to get the groups and group members of tenants that have logged into the app. I have the following permissions set up under App Registrations in TENANT A. 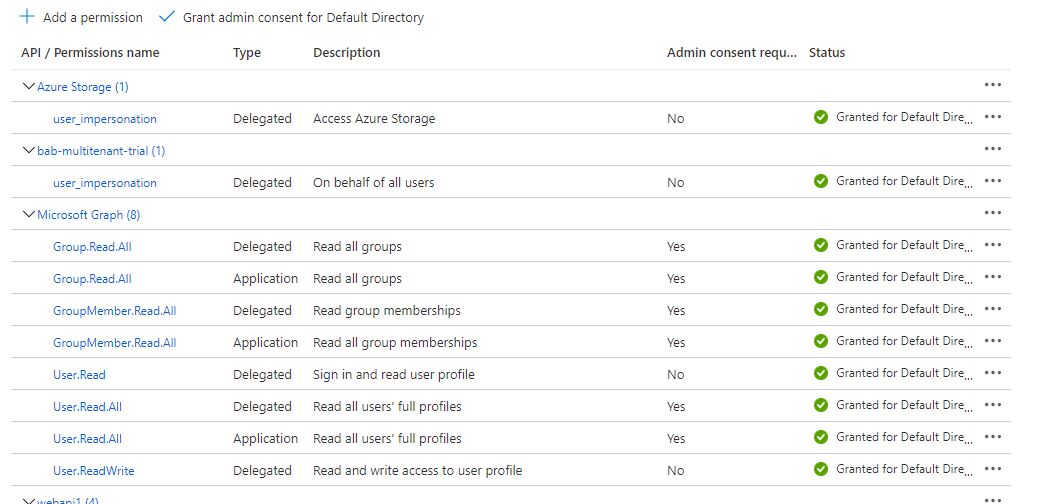
When I signed into the app as an admin user from TENANT B, I had to grant consent for the permissions and login worked as expected.
I want to be able to see all groups/members of TENANT B. I am not sure how to do this. I have tried following the explanations 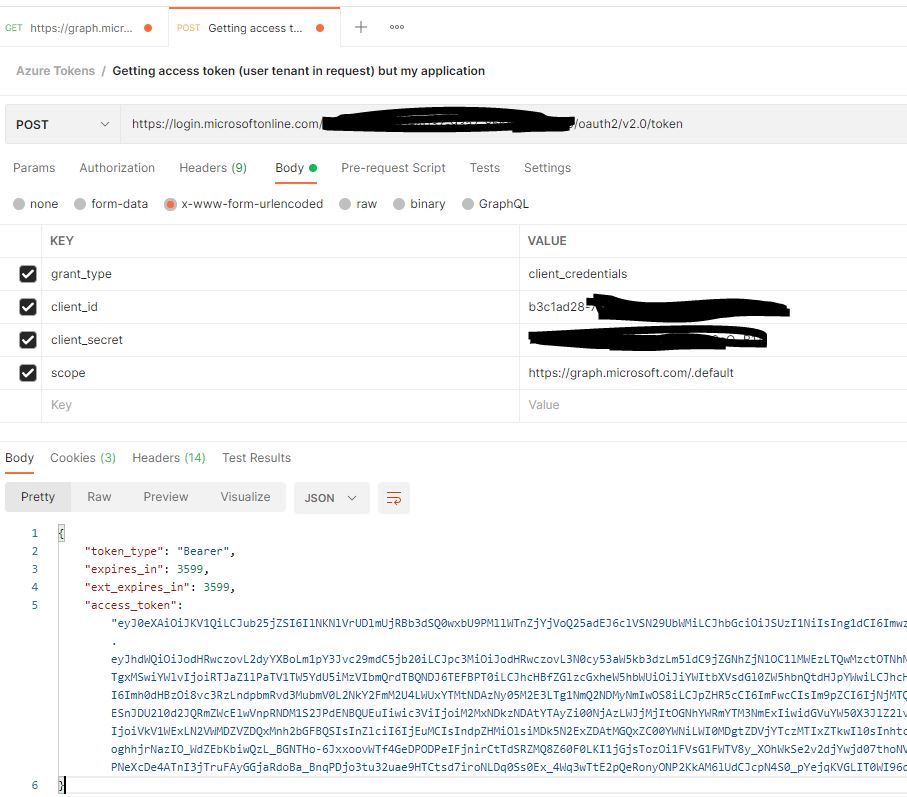
However, when I use the response token and call the Graph API 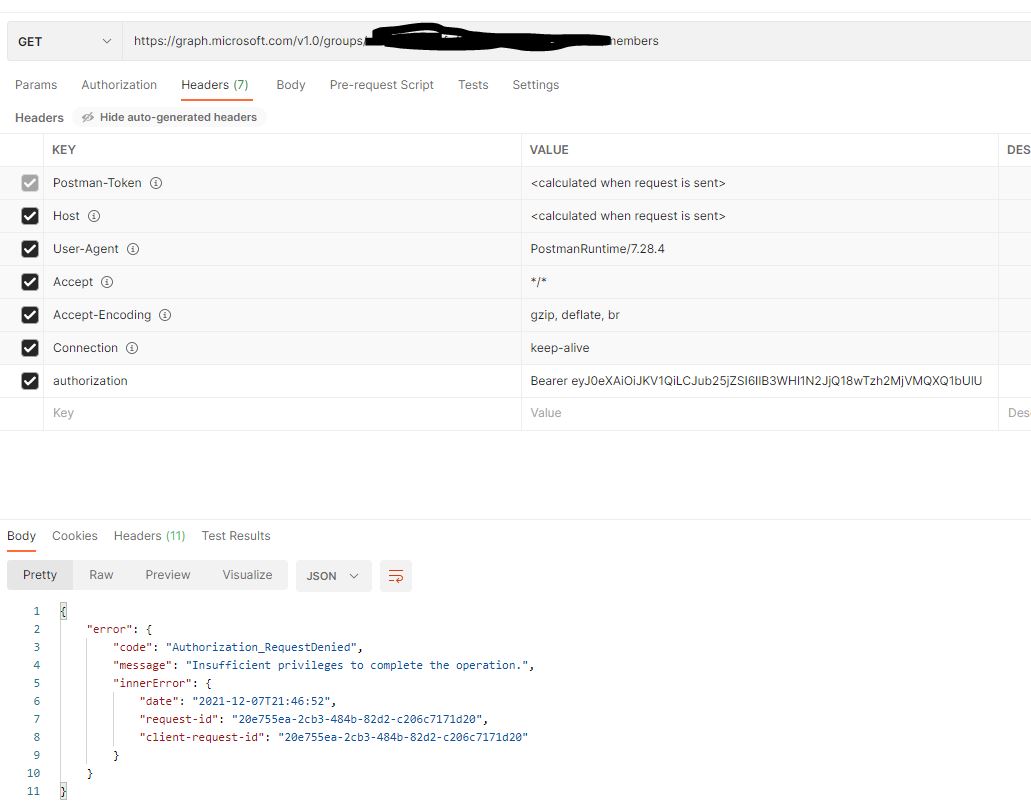
CodePudding user response:
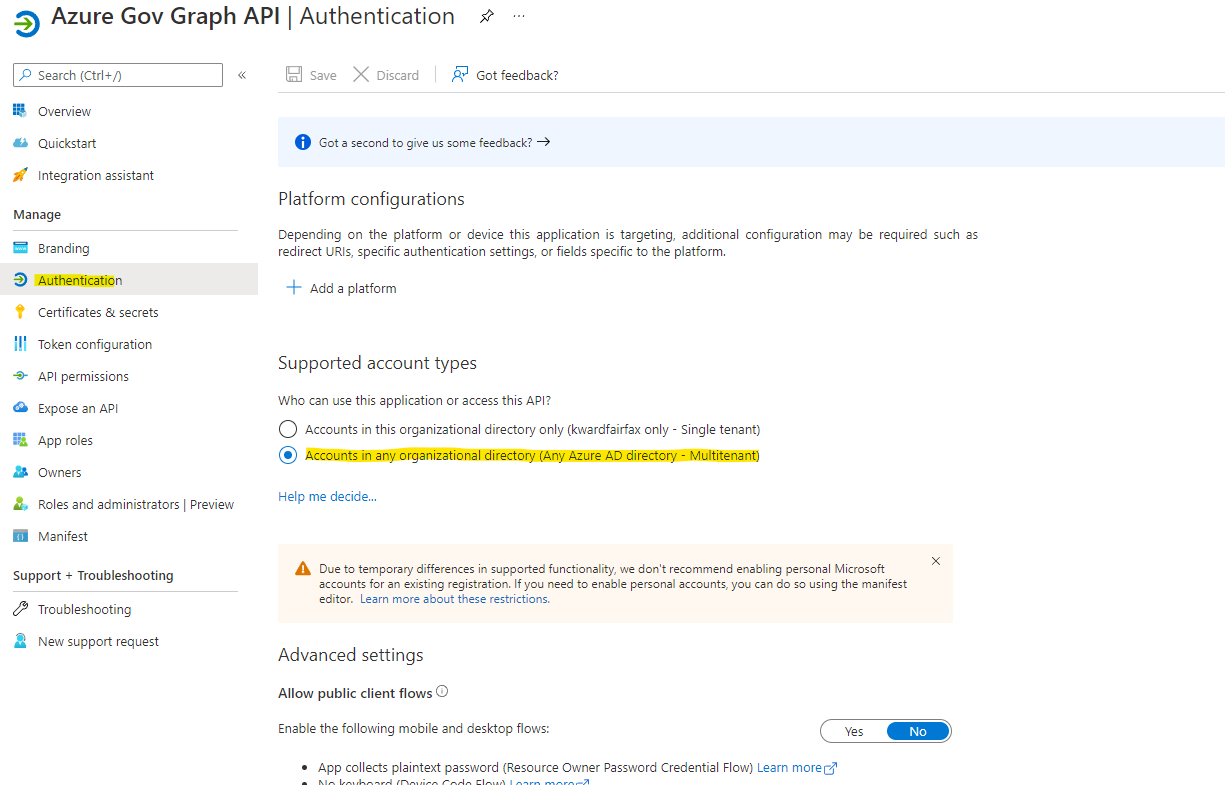
By default, web app/API registrations in Azure AD are single-tenant. You can make your registration multi-tenant by finding the Supported account types switch on the Authentication pane of your application registration in the Azure portal and setting it to Accounts in any organizational directory. (see pic below)
Before an application can be made multi-tenant, Azure AD requires the App ID URI of the application to be globally unique. The App ID URI is one of the ways an application is identified in protocol messages. For a single-tenant application, it is sufficient for the App ID URI to be unique within that tenant. For a multi-tenant application, it must be globally unique so Azure AD can find the application across all tenants. Global uniqueness is enforced by requiring the App ID URI to have a host name that matches a verified domain of the Azure AD tenant.
CodePudding user response:
You created a multi-tenant application in tenant A for generating access token and call graph api to get all the groups. When you created the app and it's consented to the api permissions, it would work for tenant A, but not for tenant B as this app hasn't registered in tenant B and got the consent. You may refer to this section and grant tenant-wide admin consent by hitting the url below. Then you may check if this app appeared in the azure portal -> azure ad -> enterprise applications in tenant B and click the app -> permissions to see if it has consent.
https://login.microsoftonline.com/{tenant_id_of_tenant_B}/adminconsent?client_id={app_client-id_in_tenant_A}