I have implemented SSO for my application. I am using AWS Cognito as Service Provider and Azure AD as Identity Provider. IdP is configured through SAML in Cognito. Below is the URL generated
https://<my_custom_domain>.auth.us-east-1.amazoncognito.com/oauth2/authorize?identity_provider=<IdP_Name>&redirect_uri=<Callback_url_passed_in_Cognito>&response_type=TOKEN&client_id=<Client_Id>&scope=aws.cognito.signin.user.admin email openid profile&state=transit
In my application, when a user tries to log in initially with their MS 365 account it asks for user credentials.
But after logout from the app, if the user attempts to log in again with a different account, it is not asking the user to enter credentials or pick up an existing account. It directly makes the app login for the previous account.
Note: If in my browser there are multiple MS 365 accounts signed-in then only my app asks for which account to use. If there is a single MS 365 account present then my app uses that one without asking the user to Sign-in with a different account.
CodePudding user response:
Since you have specifically mentioned SAML for Cognito and Azure AD integration, this answer is based on that.
When SAML service provider (SP) initate a SAML auth request with Azure AD, it can specify ForceAuthn param as true. With that Azure AD should always prompt user to authenticate. Please refer this document. So that is supported in Azure AD.
But as far as I know, Cognito doesn't support to include that parameter in the SAML AuthnRequest. Same concern has raised in this question as well.
Even though I haven't tried, I think you should be able to use Sign-out flow in Cognito SAML configuration along with Azure AD single sign-out. So I believe it should sign out the user from Microsoft and should prompt for the credentials when user try to sign in again.
CodePudding user response:
I tried to reproduce the same in my environment and got the below results:
Note that:
- SSO allows users to authenticate once and access applications without re-entering credentials.
- Single Sign-On allows users log in only once to access application without having to enter the login information each time.
- Hence, if there is only a single MS 365 account present then it doesn't ask user to pick an account.
For sample, I configured SSO and tried to access below endpoint:
https://login.microsoftonline.com/organizations/oauth2/v2.0/authorize?
&client_id=XXXX
&response_type=code
&redirect_uri=redirecturi
&response_mode=query
&scope=https://graph.microsoft.com/.default
&state=12345
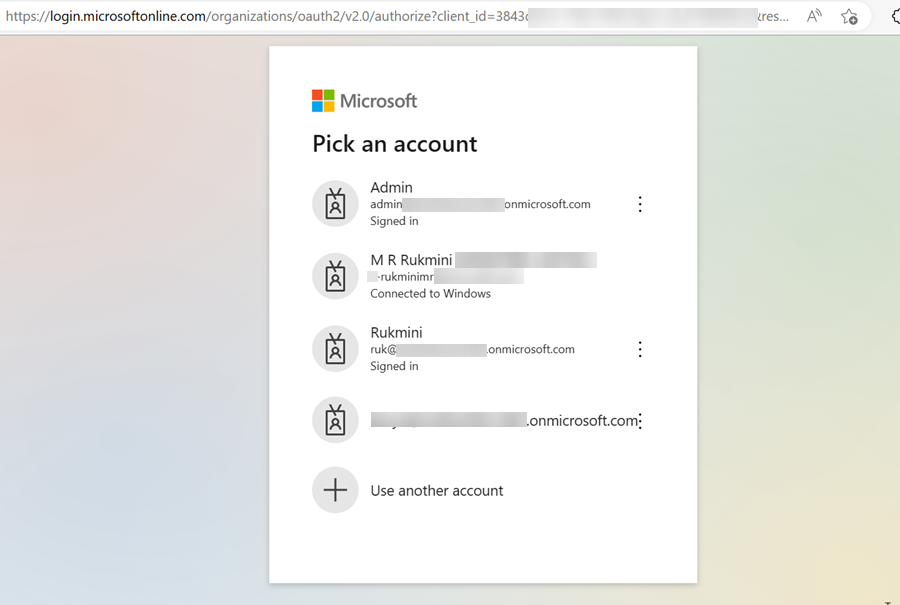
The browser prompted to Pick an account when there were multiple accounts only like below:
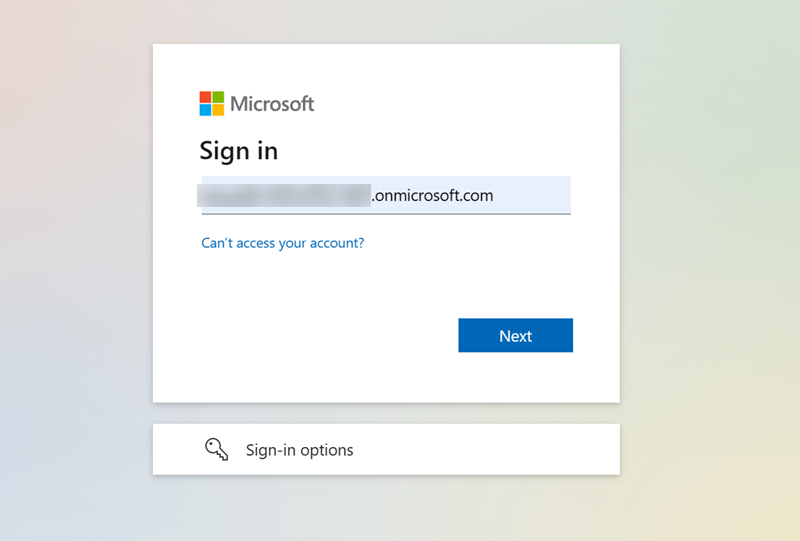
Alternatively, you can make use of prompt=login in the authorize endpoint and enter the credentials to access the application. The prompt will be appear like below:
Otherwise, to ensure the Pick an account screen try creating a conditional policy which requires multi-factor MFA) or device compliance when user try to access the Application.
Reference:
