In my studies of AWS, multiple times I have seen references to "linking" security groups. I do not understand what this means in practice. My current understanding is that when rules are defined in security groups, they are defined in terms of ports and CIDR ranges, there is no linkage to another group. So, my question is, what is this language referring to? I have a snippet from the Elasticache FAQ below with this language:
"To allow network access to your cluster, create a Security Group and link the desired EC2 security groups (which in turn specify the EC2 instances allowed) to it."
CodePudding user response:
The security group you made can be created without an EC2 instance in place. It won't have any effect if you do, but you can prepare the groups ahead of time.
Then when you have 1 or more EC2 instances (or any other resource really) you can apply 1 or more of these groups to the instances. Applying them is apparently called "linking" in your training, according to your last sentence.
To allow network access to your cluster, create a Security Group and link the desired EC2 security groups (which in turn specify the EC2 instances allowed) to it.
(emphasis mine)
Alternatively, like @luk2302 mentioned, you can also provide fine grained security by linking security groups to each other. For example: Allow traffic on port 80 of my security group only by EC2 instances who belong to <>.
CodePudding user response:
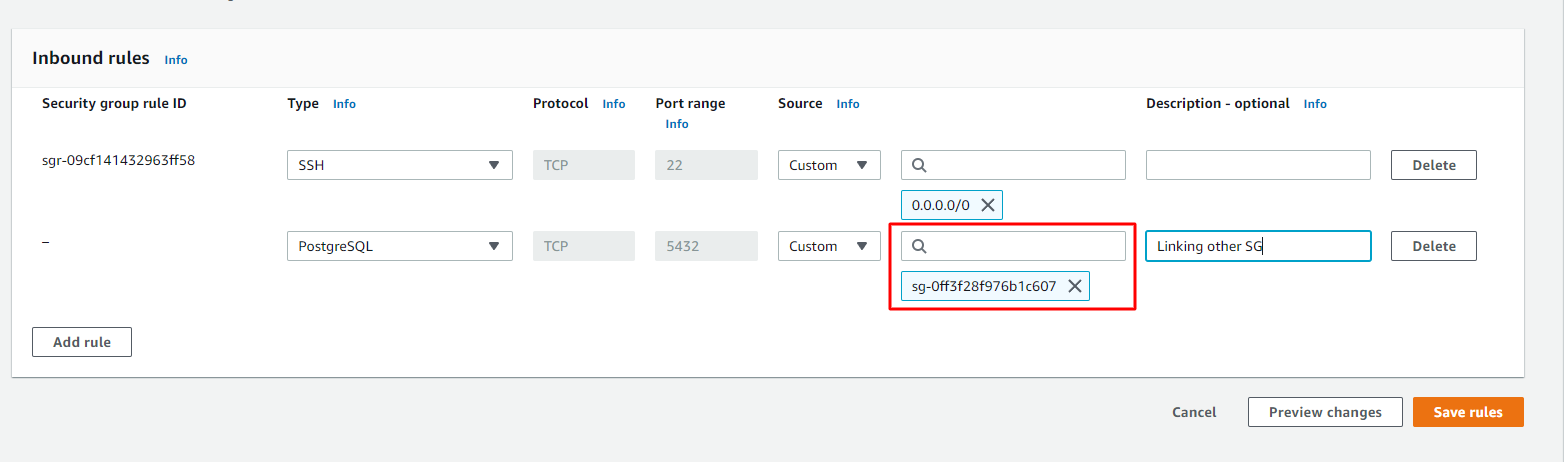
When you edit inboud/outbound rules for a Security Group, you are allowed to reference another Security Group as source/destination. Example:
The benefit of this is that you don't have rely on IP addresses or IP ranges, because these might change (instance is restarted, you want to migrate from one instance to another, etc.).
Moreover, linking a Security Group may simplify the rule table, since more than one entity can have the same Security Group attached, you don't need to specify the IP of each entity.